Guarding Against a Spectrum of Security Threats: Best Practices and Vigilance
In the ever-evolving digital world, the array of security threats is diverse and constantly mutating. This blog post delves into the multitude of security threats that organizations face and provides essential best practices and indicators to safeguard your digital assets.
**Understanding the Multifaceted Threat Landscape**
Security threats come in various forms, targeting different vulnerabilities and posing unique risks to organizations. These threats include:
- **Malware:** Malicious software designed to compromise systems, steal data, or disrupt operations.
- **Phishing:** Deceptive emails or messages aimed at tricking users into revealing sensitive information.
- **Ransomware:** Malware that encrypts data and demands a ransom for decryption.
- **Insider Threats:** Unauthorized actions or data breaches initiated by internal employees.
- **Distributed Denial of Service (DDoS) Attacks:** Overwhelming a network or system to render it inoperable.
- **Backdoors:** Hidden entry points that allow unauthorized access to systems.
- **Zero-Day Vulnerabilities:** Exploits that target undiscovered security flaws in software.
- **Social Engineering:** Manipulating individuals into divulging confidential information or taking specific actions.
- **Supply Chain Attacks:** Targeting vulnerabilities in third-party components or software used by an organization.
**Best Practices for Safeguarding Against Security Threats**
1. **Cybersecurity Training:**
- Provide regular cybersecurity training to employees to enhance their awareness of threats and best practices.
2. **Security Updates:**
- Keep all software, operating systems, and applications up to date to patch known vulnerabilities.
3. **Firewall Protection:**
- Implement a robust firewall to filter incoming and outgoing network traffic, blocking malicious content.
4. **Antivirus Software:**
- Utilize effective antivirus and anti-malware solutions to detect and remove threats.
5. **Regular Auditing:**
- Conduct frequent security audits and vulnerability assessments to identify and address weaknesses.
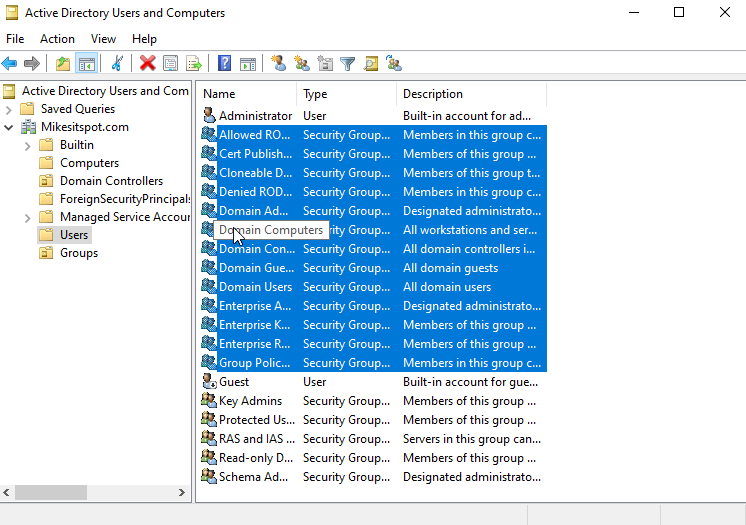
6. **Access Control:**
- Employ strict access control policies, granting permissions only on a need-to-know basis.
7. **Encryption:**
- Encrypt sensitive data to protect it from unauthorized access in case of breaches.
8. **Incident Response Plan:**
- Develop and rehearse an incident response plan to swiftly address and mitigate security incidents.
9. **User Monitoring:**
- Continuously monitor user activity to identify suspicious behavior or unauthorized access.
10. **Secure Authentication:**
- Implement multi-factor authentication (MFA) to enhance login security.
**Indicators of Security Threats**
1. **Unusual Network Traffic:**
- Monitor for unusual data flows or spikes in network traffic.
2. **Phishing Attempts:**
- Watch for suspicious emails or messages requesting sensitive information.
3. **Data Encryption Changes:**
- Unauthorized changes to data encryption settings can indicate a ransomware attack.
4. **Access Anomalies:**
- Frequent changes in user access permissions may signify an insider threat.
5. **Unexplained System Changes:**
- Sudden alterations to system configurations or files may indicate malware activity.
6. **DDoS Attack Patterns:**
- Detect traffic patterns characteristic of DDoS attacks, such as sudden traffic surges.
**Conclusion**
The multifaceted threat landscape requires a comprehensive and proactive approach to security. By implementing best practices and staying vigilant for potential indicators of threats, you can fortify your organization's defenses against an array of security challenges. In a world where cyber threats are dynamic and persistent, safeguarding your digital assets from diverse adversaries is paramount. Don't wait; start your proactive defense today and ensure the security of your digital domain.
Comments
Post a Comment