Shielding Your Perimeter: Defending Against Insider Threats for Enhanced Security
Insider threats, originating from within an organization, pose a unique and often underestimated risk to your data and security. In this blog post, we'll explore the world of insider threats, providing best practices and key indicators to help you safeguard your organization's critical assets.
**Understanding Insider Threats**
Insider threats are security risks that arise from individuals within an organization who have access to sensitive data or systems. These threats can be intentional or unintentional and may involve employees, contractors, or partners.
**Best Practices for Insider Threat Defense**
1. **User Training:**
- Provide ongoing cybersecurity training to educate employees about security risks and to raise awareness about the potential consequences of insider threats.
2. **User Access Management:**
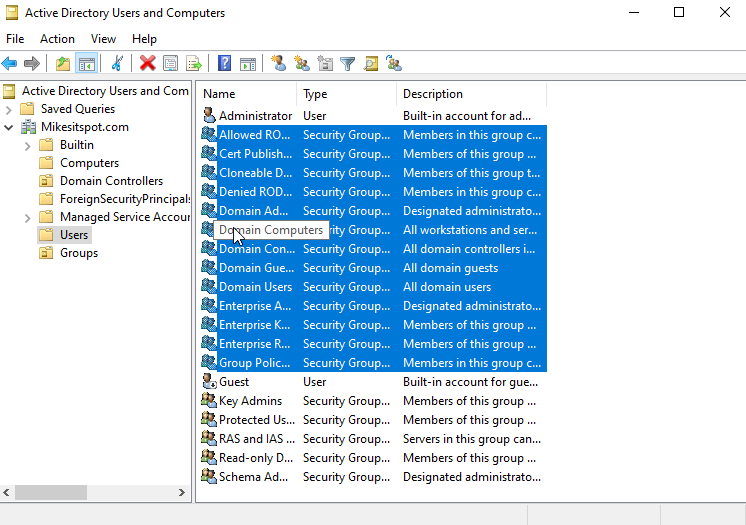
- Implement strict access controls to ensure that employees only have access to data and systems necessary for their roles.
3. **Privilege Management:**
- Employ the principle of least privilege (PoLP), granting employees the minimum level of access required to perform their tasks.
4. **Behavior Analytics:**
- Utilize user and entity behavior analytics (UEBA) to detect abnormal or suspicious user activity within your network.
5. **Data Loss Prevention (DLP):**
- Implement DLP solutions to monitor, control, and prevent data exfiltration by insiders.
6. **Regular Audits:**
- Conduct regular security audits to identify unusual access patterns, unauthorized data transfers, or unusual employee behavior.
7. **Incident Response Plan:**
- Develop and rehearse an incident response plan that outlines the steps to take in case of an insider threat incident.
8. **Whistleblower Programs:**
- Establish anonymous reporting channels to encourage employees to report suspicious behavior without fear of retaliation.
**Indicators of Insider Threats**
1. **Abnormal Data Access:**
- Unusual access to sensitive data, especially during non-business hours, can be a sign of insider threats.
2. **Unauthorized Data Transfers:**
- Monitor for unauthorized data transfers, particularly when they involve large volumes of data.
3. **Changes in User Behavior:**
- Sudden or significant changes in an employee's behavior, such as an increased interest in confidential data, could indicate insider threats.
4. **Email Anomalies:**
- Look for unusual email activity, like an employee sending sensitive information to external email addresses.
5. **Unexplained Data Loss:**
- Data loss without a clear cause or unaccounted for data changes may be indicative of an insider threat.
**Conclusion**
Insider threats are a nuanced security challenge, but with the right practices and vigilance, you can mitigate these risks and protect your organization's sensitive data. In an age where internal and external threats coexist, your proactive approach to insider threat defense is essential. Start your journey to safeguard your data and security today.
Comments
Post a Comment