Creating User accounts - Home lab 4
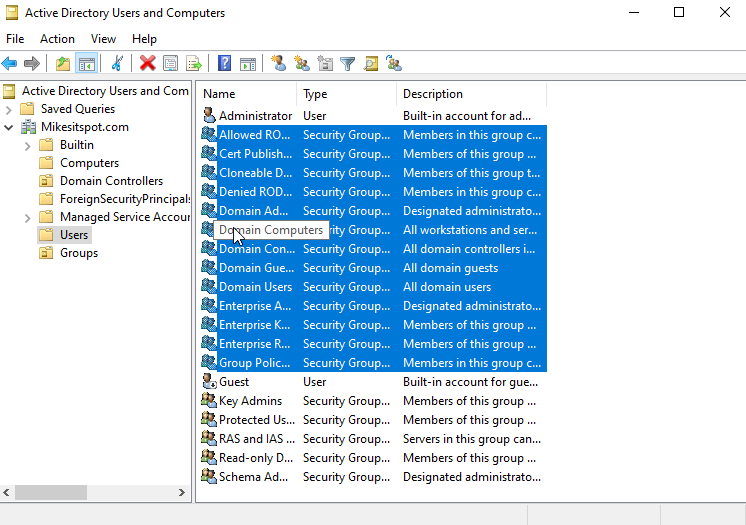
In the realm of Active Directory management, I embarked on a journey to streamline and enhance the organization of my security groups. First, I crafted a new organizational unit, elegantly named "Groups," within the Active Directory Users and Computers interface. Into this digital haven, I carefully relocated the loose security groups, leaving the Admin and Guest users comfortably housed within the Users unit. This simple restructuring not only tidied up my directory but also bestowed upon it an aesthetic simplicity, making navigation a breeze.
As I delved into the heart of the User folder, I initiated the creation of several new users for my domain. Mindful of maintaining consistency, I adhered to specific naming conventions and password settings for each new addition. This meticulous approach not only ensures a harmonious environment but also facilitates seamless navigation for future interactions.
To expedite the process for subsequent users, I employed a nifty shortcut – right-clicking on the newly created user and selecting the "Copy" option. This way, I effortlessly replicated the framework, filling in the details with efficiency and precision.
Taking another step towards efficiency, I duplicated my Admin account with a simple right-click and copy maneuver. A new service account emerged, intricately linked to a Service Principal Name (SPN) through the command prompt. This strategic move was not just an administrative task; it set the stage for future exploration—a Kerberos attack, a topic that will be delved into in a subsequent blog.
And there you have it for this blog post! In the realm of Active Directory, I orchestrated the creation of diverse user accounts, each with its own unique purpose within my evolving digital landscape. Stay tuned for the next installment, where we'll unravel the intricacies of Kerberos attacks and delve deeper into the world of cybersecurity exploration.



Comments
Post a Comment